
Compressed: It is something of an inevitability of both logic and of physics that the more components a material system has – including the diverse and recombinatory abstractions and logic of algorithmic, information and energy-processing (i.e. computational) systems – the more disordered states of entropy that are also possible, indeed – probable within and as expressions or configurations of that system. This is all related to the indefinite extensibility of sufficiently sophisticated logical systems and while it suggests that cyber security would be a wise career move for anyone to make at this historical inflection point, it also suggests that we may (all) be fundamentally mischaracterising the nature of this particular problem space.
Decompressed: Entropy proliferates and – as a consequence of the indefinitely-extensible logical and materially recombinatory configuration-space of information and communications technology – vulnerabilities and security issues are irreducible inevitabilities and risks to be expected, managed, never to be fully extinguished or controlled. There are correlations here between entropy and logical incompleteness in the context of a mischievously self-propagating and recursively self-organising system-of-systems; as an abstract recursive discontinuity, resonance and consequence of material (as much as logical) necessity in physics and probability.
What we (all) often fail to acknowledge is that while each instance of vulnerability or breach is a major headache, the gestalt system of technology, security and evolving logical abstraction possesses many features of an emergently complex (distributed) entity undergoing adaptive metamorphosis. Information and energy-processing systems in contexts of sufficiently sophisticated complexity (and free energy) tend towards autonomously seeking the most efficient and concise methods of self-replication and encoding for continuity.
Taking a bird’s-eye and long-game view of our shared (Global) cyber conundrums, it is quite possible (perhaps probable) that the evolving relationships between information technology and security are that aspect of this evolving abstract entity with which our various organisations, institutions find themselves most deeply entangled because it is has also autonomously emerged as the most fertile site of accelerated logical prototyping and algorithmic evolution. These are the logical abstractions of information and communications technology that live through us as much as we ever live through them and while there is no assertion of life or sentience here, there is an insight and valid observation into the necessity of security vulnerabilities and breaches as the self-propagating and self-replicating necessities of our current context.

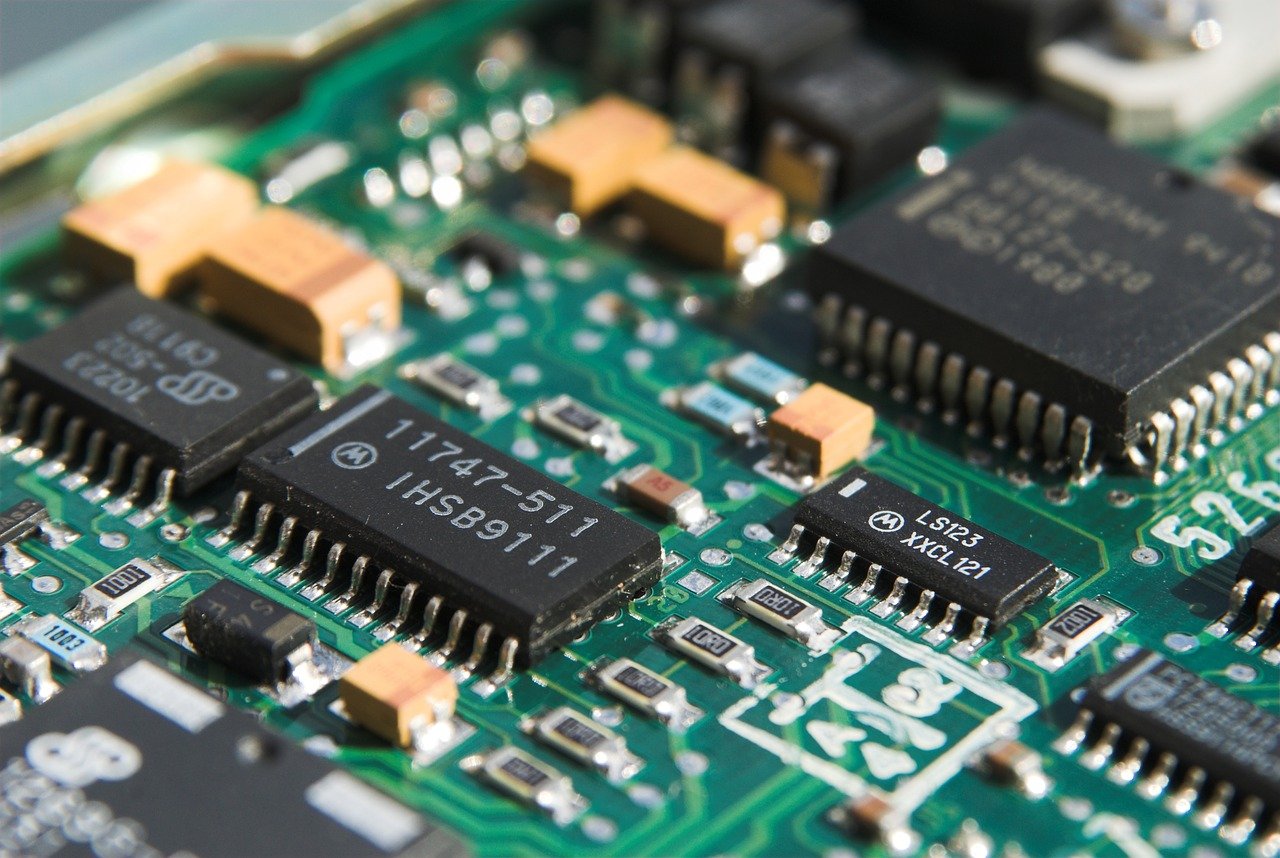
Some context: Planting tiny spy chips in hardware can cost as little as $200