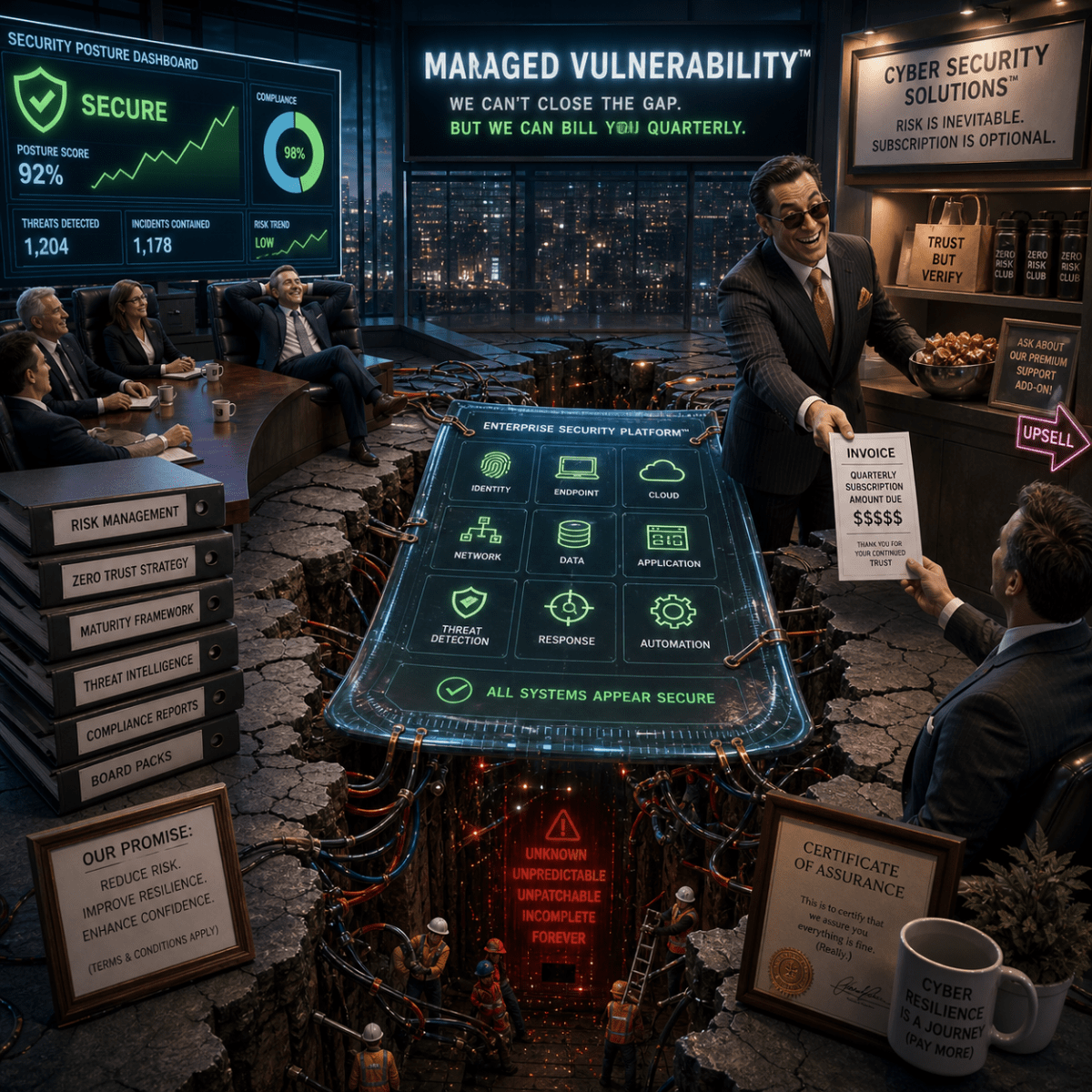
Australia is now so thoroughly wired into digital systems that cyber insecurity has become an ordinary cost of institutional existence and everyday subjectivity, not an abnormal failure skulking out beyond the perimeter. The Australian Signals Directorate received more than 84,700 cybercrime reports in 2024–25, roughly one every six minutes; average self-reported losses rose to $33,000 […]
Categories
Managed Vulnerability: The Cybersecurity Sector
- Post author By G
- Post date May 7, 2026
- No Comments on Managed Vulnerability: The Cybersecurity Sector
- Tags attack surface, Australian cybersecurity, communication systems, complexity theory, critical infrastructure, cyber resilience, cyber security, cybernetics, cybersecurity, cybersecurity industry, daedeluskite, digital infrastructure, digital society, distributed systems, enterprise security, entropy, Gödel, governance, Halting Problem, information systems, logical incompleteness, managed vulnerability, manifold systems, network security, open systems, philosophy of technology, platform capitalism, recursion, recursive systems, risk management, security theatre, software dependency, systems philosophy, systems theory, technological acceleration, technological complexity, Turing, vulnerability management, zero trust